@troyhunt : if we open a website that we've never visited before, we need browsers to show us all available details about that website, and warn us if such details are not available.
We also need better (readable) certificates identifying the responsible / accountable party for a website.
We have been lied to that anonymous DV certificates are a good idea *also* for websites we need to trust. It's a hoax.
Important: certificates never directly warrant the trustworthyness of a website. They're about authenticity, which includes knowing who the owner is and in which country they are located. This helps ensuring that you can sue them (or not, if in e.g. Russia) which *indirectly* makes better identifiable websites more reliable.
More info in https://infosec.exchange/@ErikvanStraten/113079966331873386 (see also https://crt.sh/?Identity=mailchimp-sso.com).
Note: most people do not understand certificates, like @BjornW in https://mastodon.social/@BjornW/114064065891034415:
❝
@letsencrypt offers certificates to encrypt the traffic between a website & your browser.
❞
2x wrong.
A TLS v1.3 connection is encrypted before the website sends their certificate, which is used only for *authentication* of the website (using a digital signature over unguessable secret TLS connection parameters). A cert binds the domain name to a public key, and the website proves possession of the associated private key.
However, for people a domain name simply does not suffice for reliable identification. People need more info in the certificate and it should be shown to them when it changes.
Will you please help me get this topic seriously on the public agenda?
Edited 09:15 UTC to add: tap "Alt" in the images for details.



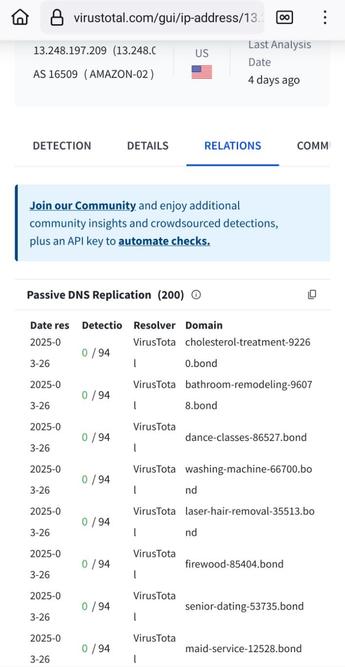
![Screenshot of https://www.virustotal.com/gui/domain/mailchimp-sso.com/relations
It shows that mailchimp-sso[.]com is "hosted" (actally proxied) by Cloudflare IP-addresses.](https://lepoulsdumonde.com/system/cache/media_attachments/files/114/229/405/523/259/382/small/7df96e02321e914a.jpeg)
![Screenshot of https://www.virustotal.com/gui/domain/mailchimp-sso.com/details
It shows that mailchimp-sso[.]com has a DV-certificate issued by "Google Trust Services".](https://lepoulsdumonde.com/system/cache/media_attachments/files/114/229/405/527/697/645/small/1db9ad39f9725666.jpeg)